Zero Trust
Fixing the cracks in zero trust
26 Mar 2026
Zero Trust in 2026
25 Feb 2026
The Zero Trust imperative for SMBs
22 Jul 2025
Unlocking the full potential of zero trust
22 May 2025
22 Jan 2025
Are you enabling a resilient workplace?Sponsored by Zscaler
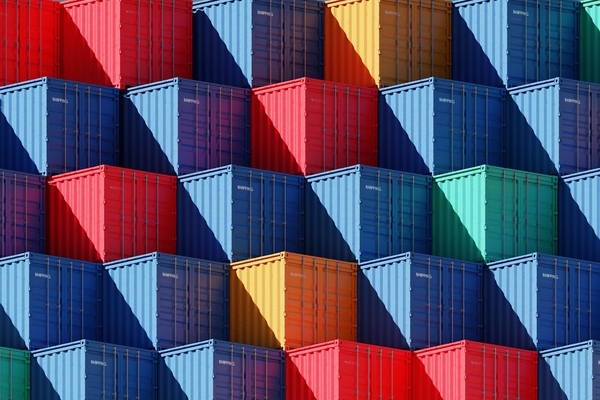
Protecting your place in the supply chain
24 Oct 2024
Managing attack surface management
13 Aug 2024
Achieving NIS2 compliance in OT environments
13 Aug 2024
The frictionless future of cyber-security
31 Jul 2024
24 Jul 2024
Zero Trust architecture and government
Most Viewed
Winston House, 3rd Floor, Units 306-309, 2-4 Dollis Park, London, N3 1HF
23-29 Hendon Lane, London, N3 1RT
020 8349 4363
© 2025, Lyonsdown Limited. teiss® is a registered trademark of Lyonsdown Ltd. VAT registration number: 830519543