Security Threats
AI is reshaping cyber-crime – and businesses are struggling to keep paceSponsored by Check Point Software
25 Mar 2026
The rise of MFA bombing
24 Mar 2026
04 Mar 2026
New rules, rising threats: why lean IT teams must rethink cyber-securitySponsored by CORO CYBER SECURITY
The evolution of phishing
29 Jun 2023
The continued evolution of phishing
19 May 2023
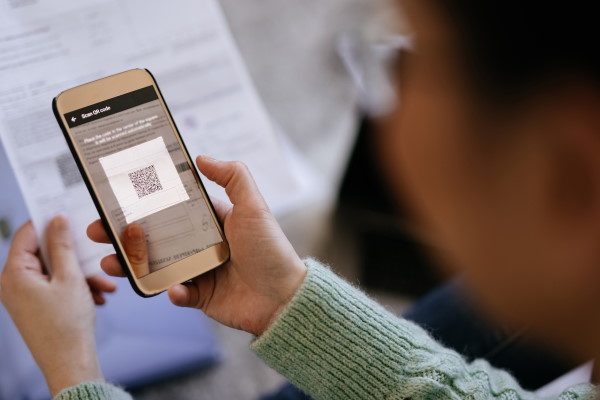
The rising threat of QR code attacks
19 Jan 2022
01 Dec 2025
The Expert View: Securing the AI-Driven WorldSponsored by Checkpoint
Most Viewed
Winston House, 3rd Floor, Units 306-309, 2-4 Dollis Park, London, N3 1HF
23-29 Hendon Lane, London, N3 1RT
020 8349 4363
© 2025, Lyonsdown Limited. teiss® is a registered trademark of Lyonsdown Ltd. VAT registration number: 830519543