teissAwards2026
The teissAwards2026 recognise excellence in cyber and information security, with a particular focus on the contributions of vendors and technologies in relation to the use, development, and deployment of information security in the past 12 months.
The categories within the teissAwards2026 are assessed by an independent panel of distinguished judges, and the winners will be announced at the teissAwards2026 gala dinner, held on the 26th February 2026.
The teissAwards2026 are part of a broader portfolio of information security events, which have taken place over the last decade, and represents the largest and most comprehensive cyber security gathering of experts in Europe.
Judging Information
For more information about the teissAwards2026, please get in touch with us on awards@teiss.co.uk
Key Dates
Here are all the key dates you need to know for the teissAwards2026!
1st July 2025 – Submissions open
7th December 2025 – Entry Submissions close
26th February 2026 - teissAwards2026 winners announced!
Finalists
The teissAwards2026 has 19 categories that celebrate the achievement of cyber security vendors over the last 12 months. Please see our finalists below:
Awards Categories
Select a category to learn more about it.
- Best Cloud Security Solution
- Best Email Security Solution
- Best Incident Response Solution
- Best Endpoint Security Solution
- Best AI Security Solution
- Best Threat Intelligence Technology
- Best Vulnerability Management Solution
- Best Human Risk Solution
- Best Penetration Testing Solution
- Best Security Compliance Solution
Categories
Best Email Security Solution
The entrant must be an email security vendor who offers a solution that safeguards the privacy of email messages by filtering against spam, malware and other malicious emails, while providing integrated protection against sophisticated email attacks.
Finalists
Red Sift
TrustLayer
Best Incident Response Solution
The entrant must be an incident response provider with a service or software that provides users with the tools to identify and respond to security breaches, as well as reporting and analysing incident data.
Finalists
Illumio
LRQA
Orange Cyberdefense
Performanta
Solis
Splunk
Thrive
Best Threat Intelligence Technology
The entrant must be a threat intelligence technology supplier whose solution or product provides organisations with timely intelligence on the latest cyber-threats affecting their IT infrastructure, as well as techniques to combat these threats.
Finalists
BlackFog
Cyble
Ivanti
Performanta
Solis
ThreatMatch
Best Human Risk Solution
The entrant must be a security awareness training and/or bahavioural science specialist offering ready-to-use security training and awareness campaigns and/or behavioural science to better equip organisations against real-world cyber-threats.
Finalists
Cyberguardian
CybSafe
ISACA
KnowBe4
Outpost24
OutThink
Redflags
Best Security Compliance Solution
The entrant must be a security compliance vendor whose product enables organisations to manage their security processes, systems and policies to identify areas of compliance and non-compliance.
Finalists
CyberSmart
ISMS.online
Kiteworks
Obrela
Performanta
Quod Orbis
SureCloud
Tufin
VikingCloud
Best New Launch Product
The entrant must be a security vendor with a new product or service focused on protecting organisations’ networks, systems and applications from threats. The product or service must have been launched after 1 July 2024.
Finalists
Abnormal AI
comforte
Forcepoint
Forescout
Illumio
Mindsprint
Solis
Cyber Security Company of the Year
Entrant must be a cyber-security company with a demonstrable history of offering enterprise-level innovative and comprehensive cyber-security solutions with a significant growth in adoption, client base or product/service effectiveness over the past 12 months.
Finalists
Bridewell
Cato Networks
CyberSmart
CyXcel
Goldilock Secure
Gritera Security
Intigriti
ISC2
Keeper Security
KnowBe4
LRQA
Obrela
Performanta
Quod Orbis
SecurityScorecard
Solis
Splunk
ThreatLocker
Thrive
TrustLayer
Wiz
Best Emerging Security Technology
The entrant must offer an emerging security technology including AI/ML, blockchain, IoT and quantum computing aimed at enabling organisations to enhance their security posture, mitigate potential risks and safeguard sensitive data.
Finalists
Confidencial
Huntsman
Security Salt
Security Wire
Judges
Our judges are industry-renowned experts in their field. Each brings their expertise to bear to judge the teissAwards2026.
Judges

Thom Langford
Founder, (TL)2 Security
Thom is an industry engaged and sought after information security subject matter expert and speaker. Currently the EMEA CTO for Rapid7, Thom collaborates with customers, businesses and the media as a whole, further exploring his passion of communicating and educating on information security topics to audiences through storytelling, humour and plain language.
He founded (TL)2 Security to offer strategic information security consultancy that focuses on Virtual CISO, strategic business alignment and public speaking/advocacy for hire. Thom has also been Chief Information Security Officer at Velonetic (insurance) and Publicis Groupe (communications and marketing), building global teams and security capabilities from the ground up.
An international public speaker and award-winning security blogger and podcaster, Thom is also the sole founder of Host Unknown, a loose collective of three infosec luminaries combined to make security education and infotainment films. Google is your friend if you want to find out more about Thom.

Lisa Ventura
Editor & Founder, Cyber Security Unity
Lisa is a keynote speaker, moderator and panellist, and has taken part in numerous conferences and events, both in-person and virtual. She is often asked to write articles, blogs and press features about cyber security, neurodiversity, mental health issues and more.

Danny Dresner
Professor of Cyber Security, University of Manchester
Danny is a respectable Professor of Cyber Security at the University of Manchester and a Fellow of the Institute of Information Security Professionals. Whilst at the NCSC, he created the core of SANS' training for BS 7799, edited national security breaches surveys, and wrote the first standards for source code escrow. He has contributed to books, conferences, and appeared on numerous TV channels including the BBC.

Steve Furnell
Professor of Cyber Security, University of Nottingham
Steven is a Professor of Cyber Security at the University of Nottingham. His main research interests are broadly linked to the intersection of human, technological and organisational aspects of cyber security, and has authored over 330 papers in refereed international journals and conference proceedings, as well as various books, chapters, and professional articles.

Edd Hardy
Director of Cyber security, AlixPartners
Edd has worked in most roles in cyber, from pentesting and audit through to risk management and CISO roles.
He is a highly experienced consultant, manage cyber risk to enable organization growth and security. Working with investors and the C-suite to ensure security is adding value to the organization.
He has helped large organizations transform their cyber programs from reactive functions that inhibit the business into proactive value creating teams. Not only aligning cyber with the organizations risk requirements but using it to deliver business objectives, create flexibility and enable the organization to safely embrace risk.

Andrea Cullen
CEO & Co-Founder, CAPSLOCK
Andrea has years of industrial experience as a computer programmer and systems analyst working on projects throughout the UK where she has been responsible for the development and implementation of many software systems. She co-authored, developed, and delivered the GCHQ-certified Cyber Security Master’s degree at the University of Bradford, and is also the Co-founder and Head of Research & Development at CAPSLOCK.

Paul Watts
Distinguished Analyst, Information Security Forum
Paul is a senior Information Security and Technology professional with over twenty-six years’ experience covering vertical markets including Transportation, Banking and Finance, Manufacturing, Retail and Telecommunications both in Europe and the UK. He was named as one of the top 100 global CISOs in the HotTopics.ht “CISO 100 2017” in 2017 and 2020.

David Cartwright
CISO, Santander International
Dave has been based in Jersey since 2009, and is presently head of IT security for an international bank. He is the co-founder and chairman of the Jersey Charitable Skills Pool; deputy chairman of the Channel Islands Information Security Forum; a committee member of the Jersey branch of the BCS; and the Digital Committee of the Jersey Chamber of Commerce.

Ed Tucker
CyberSecurity CTO, Telefonica Tech
Ed is a recognised expert, with a rich history of creating high performance teams, world class capabilities, driving business resilience and confidence. He is a pragmatic, yet passionate individual with a demonstrable record of defining and executing transformational change into businesses of varying maturities.

Jonathan Craven
Data privacy and cyber security consultant, XRHA
promote better governance and security processes and behaviours.

Paul Holland
Cyber Capability Manager, Royal Mail

Stuart Frost
Head of Enterprise Security and Risk Management Department for Work and Pensions (DWP)
Stuart has won multiple industry global awards for his work in the GRC space and is adept at integrating all security disciplines to enable a holistic approach in support of business objectives. He was named as one of the UK’s top 50 Tech Leaders and a top 30 Transformational Change Leader in May 2024 for his role in driving innovation and change across the security sector.
He was awarded the British Empire Medal (BEM) in 2017 for his services to the local community and in 2023 was also the proud recipient of the Coronation medal in recognition of his security input to the Coronation of King Charles III.
Chuck Brooks
Adjunct Professor, Georgetown University
Chuck Brooks serves as President of Brooks Consulting International. He also serves as an Adjunct Professor at Georgetown University, teaching graduate courses on risk management, and cybersecurity.
Chuck was named “Top 5 Tech Person to Follow" by LinkedIn” where he has almost 118,000 followers on his profile.he also owns and manages 10 LinkedIn security oriented groups.As a thought leader, blogger, and event speaker, he has briefed the G20 on energy cybersecurity, the US Embassy to the Holy See and Vatican on global cybersecurity cooperation. He has served on two National Academy of Science Advisory groups, including one on digitalizing the USAF, and another on securing BioTech. He has also addressed USTRANSCOM on cybersecurity and serves on an industry/government Working group for CISA focused on security space systems.
Chuck's is also a contributor to Forbes, The Washington Post, Dark Reading, Homeland Security Today, Security Information Skytop Media, GovCon, Barrons, The Hill, and Federal Times on cybersecurity and emerging technology topics. He has 57,000 subscribers to his newsletter "Security and Tech Insights." He is also the author of two books on cybersecurity and tech coming out this year.
Chuck has received presidential appointments for executive service by two U.S. Presidents, and served in executive leadership roles at public companies General Dynamics, Xerox, and Rapiscan.
He has an MA from the University of Chicago, a BA from DePauw University, and a certificate in International Law from The Hague Academy of International Law.

Keil Hubert
Head of Security Awareness & Training, OCC
Keil Hubert is the head of Security Training and Awareness for OCC, the world’s largest equity derivatives clearing organization, headquartered in Chicago, Illinois. Prior to joining OCC, Keil has been a U.S. Army medical IT officer, a U.S.A.F. Cyberspace Operations officer, a small businessman, an author, and several different variations of commercial sector IT consultant. Keil deconstructed a cybersecurity breach in his presentation at TEISS 2014, and has served as Business Reporter’s resident U.S. ‘blogger since 2012. His books on applied leadership, business culture, and talent management are available on Amazon.com. Keil is based out of Dallas, Texas.
He knows he is only as good as the teams he leads, so he takes time to train, coach, and mentor each person for career growth and success, As a result, can create an environment of cohesion with optimal performance.
His key areas of expertise include Strategic Planning & Execution, Cyber Security, Financial Management, Policy Development & Execution, Project Management, Fraud Management, Staff Development & Leadership, ISO27001, NIS-OES, PCI/DSS & SoX, SOC/SIEM/SIAM/SOAR, ISO25999, NIST CSF, UK/EU Data Protection/GDPR and FCA/EBA Regulation.

Edewede Oriwoh
Group IT Information and Cyber Security Manager, Zigup Plc
Edewede has worked in various areas of Information and Cyber Security including in Data, Identity and Access Management, Asset, Cloud, Vulnerability Management, Cyberphysical, Security Awareness, Threat Hunting and Threat Intelligence, Incident Management and Disaster Recovery, among others. She has a keen interest in Proactive, Continuous, Responsive and Reactive Security.
She encourages the support of end users with security awareness guidance, well-configured and managed tools as well as clear Policies, Processes and Procedures so they can play their part as an essential link in any organisation's Cyber Security chain.
She also promotes the importance of remembering the fundamentals such as making security a habit and, more broadly, remembering that, "If it does not exist, there's nothing to secure".

Sandra Bell
Experienced Cyber Security Leader
Sandra is an experienced leader with over 30 years’ experience of helping organisations develop the skill, will and grit to succeed regardless of what happens. She has a track record of facilitating organisations achieve and maintain standards together with firsthand experience of managing crisis, emergency and disaster recovery activities.
Sandra is also a strong influencer who is able to rapidly assimilate complex regulatory and stakeholder environments and ensure risk and compliance solutions are intimately aligned to corporate strategy. An excellent communicator and business builder who has created and led successful business units and consulting practices.

Edward Starkie
Director of Cyber Risk, Thomas Murray
Edward is confident in his ability to engage effectively with both technical experts and Board-level stakeholders and ultimately deliver tailored services that empower organisations to identify, assess, and sustainably manage cyber security risks in a pragmatic, results-driven manner.

Moona Ederveen-Schneider
Advisory Board Member, Cyber London
Moona Ederveen, is a Board Advisor and Innovative Tech Influencer, and most recently, served as Executive Director EMEA in financial services. Visiting international security conferences from age 16, she consulted at global banks and advised on cyber security and risk for nearly two decades. As a multi-lingual brand ambassador to financial services, other sectors, and government stakeholders, she is an avid builder of trusted communities. A strong advocate for cross-sector crisis preparedness and resilience, she also works to encourage the next generation of talent into tech careers.

Lessie Skiba
Deputy Managing Director, Cyber Readiness Institute

Laurie Gibbett
Managing Cyber Security Consultant, Eraneos UK Ltd.
Laurie is creative at heart, so like to incorporate visual design into her personal and work life. She has an eye for detail however, she likes to bring out key messages and present the bigger picture. She has a strategic approach to most things and purposefully get involved in projects outside her day-to-day work on deals to ensure, she is
working on the strategy of the security business unit, implementing initiatives for purposeful change.

Janet Bastiman
Chief Data Scientist, Napier AI

Dom Lucas
Head of Security Technology and Security, British International Investment plc
Dom is Head of Security for British International Investment', the UK's Development Finance Institution. He leads on both security strategy and security operations and has responsibility for cyber, information, physical and travel security. Dom has a broad experience across cyber security having worked across wide range of public and private institutions. Prior to joining BII, Dom led the client facing security assurance functions for several Magic Circle Law Firms, whilst he has previously held the position of Cyber Specialist Supervisor within the FCA, overseeing the cyber resilience preparedness of UK retail Banks. Dom has a background in Law Enforcement and is currently a member of the Chartered Institute for Information Security and the Security Institute.

Satyam Rastogi
Director of Information Security & DevOps, BAMKO
He is responsible for safeguarding BAMKO’s digital assets in accordance with ISO 27001, SOC 2, GDPR, CCPA, and PCI DSS standards whilst bolstering their cybersecurity posture. His role involves leading dedicated teams in vulnerability assessments, penetration testing, and the vigilant monitoring of infrastructures to pre-empt risks and ensure compliance.
Ceremony & Tables
teissAwards2026 will take place on the evening of the 26th of February 2026, immediately after teissLondon2026 | The European Information Security Summit.
Both the summit during the day and the awards in the evening will be held at Convene, 155 Bishopsgate, Liverpool Street, London, EC2M 3YD.
Our table sales programme is now open. For all enquiries please email Norik at n.riza@teiss.co.uk
Book Seats
Individual seats are available at £524 per seat and include:
- Welcome sparkling wine
- 3 course dinner
- Awards ceremony
- Wine, beer, soft drinks with dinner
SOLD OUT
Standard tables are available at £4195 per table and include:
- Welcome sparkling wine
- 10 seats for you and your colleagues
- 3 course dinner
- Awards ceremony
- Wine, beer, and soft drinks with dinner
SOLD OUT
We have two VIP tables available at £4720 per table and includes:
- Welcome champagne
- Preferential position in the awards room
- 10 seats for you and your colleagues
- 3 course dinner
- Awards ceremony
- Winer, beer, soft drinks with dinner
SOLD OUT
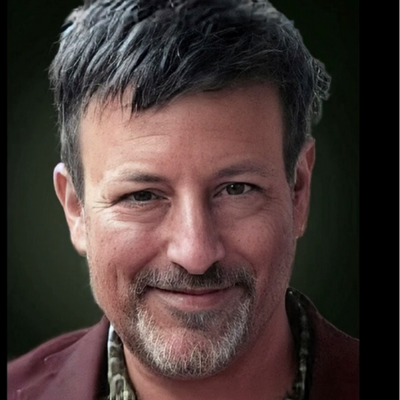
Our Host
 Andrew Maxwell is an Irish stand-up comedian recognisable as the narrator of the long-running MTV series Ex On The Beach and as a regular on The News Quiz. He has also hosted his own BBC Radio 4 shows Andrew Maxwell's Public Enemies and Welcome To Wherever You Are.
Andrew Maxwell is an Irish stand-up comedian recognisable as the narrator of the long-running MTV series Ex On The Beach and as a regular on The News Quiz. He has also hosted his own BBC Radio 4 shows Andrew Maxwell's Public Enemies and Welcome To Wherever You Are.FAQ
Find a list of our most frequently asked questions below. Got a question that isn’t on this list? Drop us a line at awards@teiss.co.uk and we’ll get right back to you.
How are the awards organised?
There are 19 Categories within the teissAwards2026, all focused on recognising excellence amongst the information security vendor market.
Who is eligible?
The teissAwards2026 are open to all information security product, service and training providers. Each Category has defined eligibility criteria and guidance on who should apply.
How can we enter?
For each Category, there are a set of questions you must answer in order to make your Round 1 Submission. Your organisation is allowed to enter as many categories as are applicable to you.
You will then need to submit your Round 2 video recording.
Please download our Entry kit for full information on entering the teissAwards2025.
Where do we enter?
Entry is done via this site, by clicking “Enter now” and following the instructions. You can start and save your entries before submitting.
Who decides if we’ve won?
A select panel of industry experts make up our judging panel. Their details can be seen on the following pages. They will score all submitted entries that are shortlisted.
How much does it cost to enter?
Entry is free.
What are the deadlines for entry?
1st July 2025 – Submissions open.
7th December 2025 – Entry Submissions close
26th February 2026 - teissAwards2026 winners announced!
You must submit your Entry before midnight on 7th December 2025.
Contact
To find out more about teissAwards2026, please contact:
Submissions Manager:
Joseph Yiadom | awards@teiss.co.uk
Sponsorship Sales Manager:
Marc Morrow | T: +44 (0)20 8349 6453 | M: +44 (0)7977 926736
Sponsorship Sales Manager:
Grant Scheffer | T: +44 (0)20 8349 6478 | M: +44 (0)7811010102
Sponsorship Sales Manager:
Jean-Philippe Le Coq | T: +44 (0)20 8349 5592 | M: +44(0)7494 705170